Table of Contents
HIPAA or Health Insurance Portability and Accountability Act of 1996 focuses on protecting Protected Health Information (PHI). This law established national standards on how covered entities, health care clearing houses, and business associates share and store PHI. HIPAA-compliant medical transcription ensures that sensitive patient data remains confidential, preventing unauthorized access, use, or disclosure. Non-compliance can result in severe legal consequences, reputational damage, and compromise patient confidentiality. Practices must outsource only to HIPAA-compliant medical transcription companies to ensure safety and confidentiality of patient data. Outsourcing transcription tasks helps to minimize the burden on physicians related to EHR documentation. Ensure that the chosen transcription vendor is well aware of the regulations of HIPAA. By strictly following HIPAA guidelines, transcription services contribute to maintaining patient trust, safeguarding privacy, and upholding the integrity of the healthcare system.
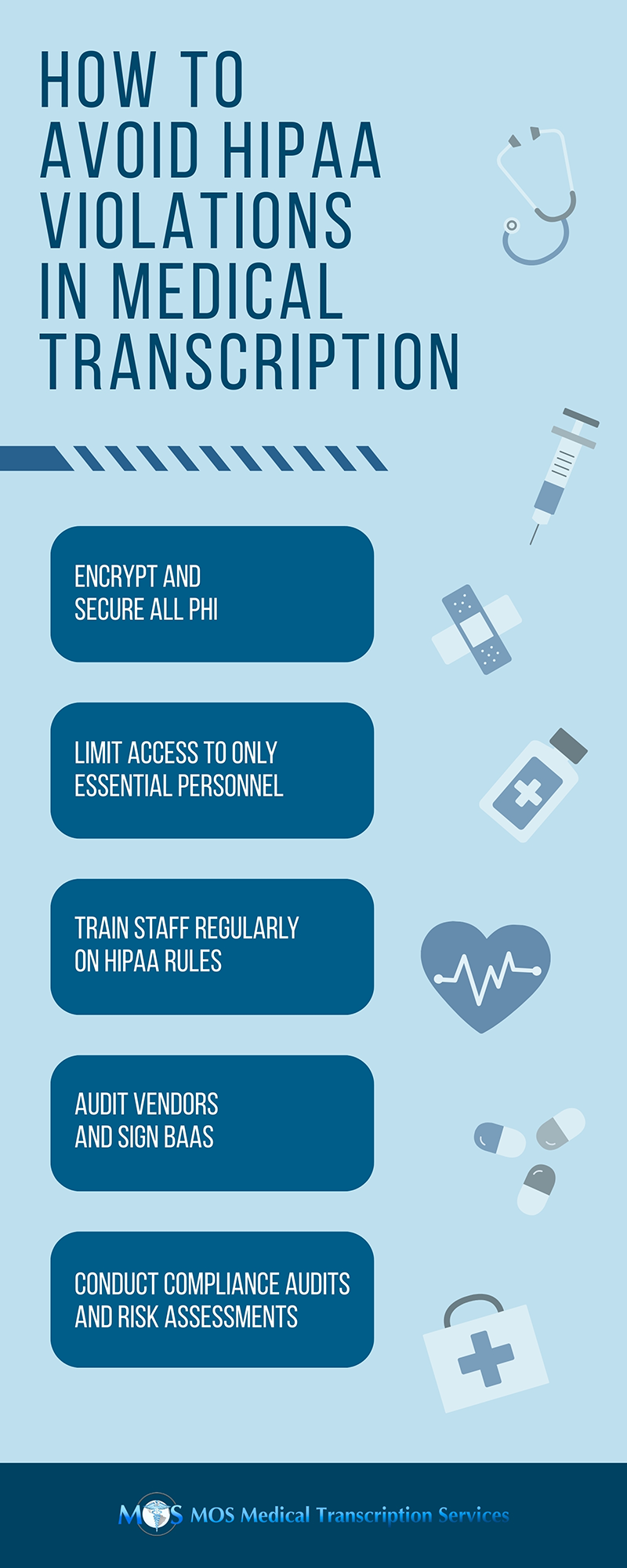
5 Key HIPAA Rules for a Medical Transcription Company
The following are the five main HIPAA rules to understand:
1. Security Rule: This rule regulates the standards, procedures and methods regarding the safety of electronic Protected Health Information (PHI) on storage, accessibility and transmission. There are three levels of security here which are as follows:
- Administrative Requirements: These are rules that ensure that the patient data is accurate and accessible to authorized people. Following are its privacy procedures:
- Assign an executive to oversee data security and HIPAA compliance.
- Identify the employees that have access to patient data.
- Train employees about the privacy policy of your organization and how it applies to their job.
- Require all outside parties who need to access protected patient data to sign contracts stating that they will comply with HIPAA security rules.
- Back up data and keep an emergency plan ready in case of disasters that could cause information loss.
- Conduct an annual data security assessment.
- Develop a data breach response plan that addresses affected patients and resolving compromised IT systems.
- Technical Security Requirements: These are measures that protect your networks and device from any breaches:
- Protect your sensitive files by encrypting them when sending them via email and make sure that any cloud-based platform you use has encryption.
- Authenticate data transfers to third parties with password, a two- or three-way handshake, a token, or a call back.
- Require that employees periodically change their passwords, and ensure passwords contain a mix of letters, numbers, and special characters.
- Protect your network from any kind of hacking and other breaches with firewalls and intrusion detection systems.
- Train your employees so that they can identify and avoid phishing scams.
- Prevent data entry mistakes by using double-keying, checksum, and other redundancy techniques.
- Keep updated documentation of your organization’s technology and network configurations.
- Physical Requirements:These rules help your organization prevent physical theft and loss of devices that contain patient information.
- Limit patient access to computers by keeping them behind counters, secured to desks, and away from the general public.
- Restrict access to secure areas, monitor building safety, and require visitors to sign in.
- Be cautious and follow best practices when upgrading or disposing of hardware and software, or even when securely wiping hard drives.
- Train employees and contractors about physical safety best practices, and make them understand the importance of securing their cell phones and mobile devices.
2. Privacy Rule: It protects the PHI and medical records of all the patients. It also limits and has conditions on different uses and disclosures that can be and cannot be made without the authorization from the patients. This rule permits the patients to have a copy of their records and also request for corrections to their file. Request of Access to Protected Health Information (PHI); Notice of Privacy Practices (NPP) Form; Request for Accounting Disclosures Form; Request for Restriction of Patient Health Care Information; Authorization for Use or Disclosure Form; and the Privacy Complaint Form are some of the specific forms that concur with this rule.
3. Identifiers Rule: There are three unique identities that HIPAA identifies for those who use HIPAA -regulated financial and administrative transactions, National Provider Identifier (NPI), a 10-digit number used for covered healthcare providers in every HIPAA administrative and financial transaction, National Health Plan Identifier that identifies health plans and payers under the Center for Medicare & Medicaid Services (CMS), and the Standard Unique Employer Identifier which identifies employer entity in HIPAA transactions.
4. Enforcement Rule: This is an extension of HIPAA Privacy and Security Rule that increases the penalties in case of any violation. This rule focuses on five areas, and is relevant to covered entities and business associates:
- Application of HIPAA security and privacy requirements
- Establishment of mandatory federal privacy and security breach reporting requirements
- Development of new privacy requirements and accounting disclosure requirements and restrictions on sales and marketing
- Establishment of new criminal and civil penalties, and enforcement methods for HIPAA non-compliance
- A stipulation that all new security requirements should be included in all Business Associate contracts.
5. Transactions Rule: This rule deals with the transactions and code sets used in HIPAA transactions. It includes ICD-9, ICD-10, HCPCS, CPT-3, CPT-4 and NDC codes, and these codes should be used accurately to ensure accuracy, safety and security of medical records and PHI.
Outsourcing to HIPAA-compliant Medical Transcription Service
While outsourcing the transcription task, it is important for healthcare organizations to ensure that the chosen transcription vendor is well aware of the regulations of HIPAA.
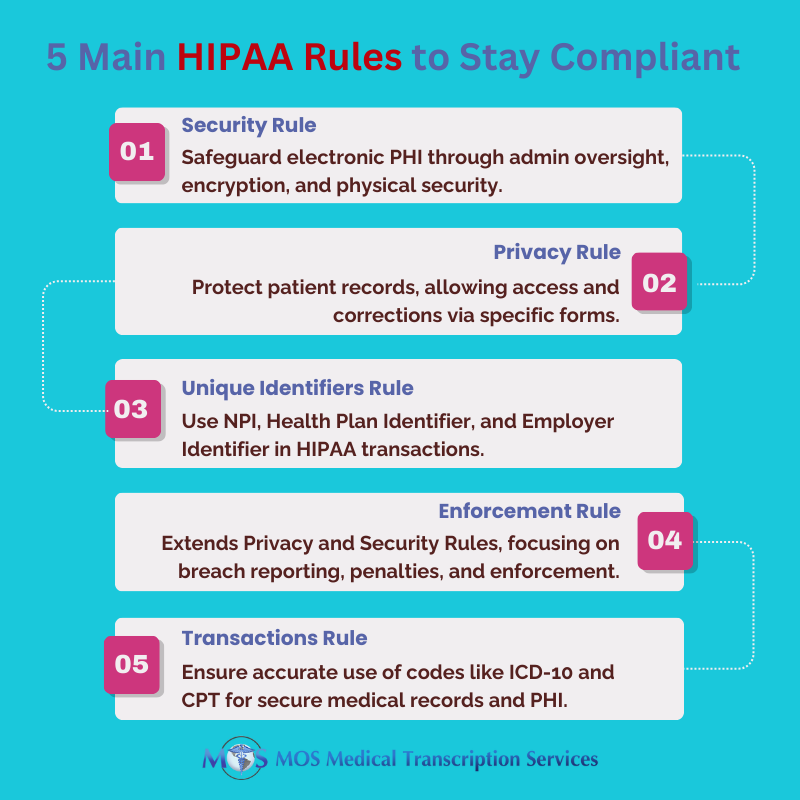
Following are some of the measures that medical transcription services take to be HIPAA compliant.
- All transcription files that contain vital healthcare information are encrypted, so that only authorized personnel can access the files.
- All medical transcriptionists are made aware of non-disclosure and privacy agreements before taking up the project, and the transcription work begins only after the required clearance.
- No external subcontractors have access to transcription files or handle medical transcription.
- It is ensured that all networks are protected with internal transcriptionists and use of password-protected computers. The software is also protected with the latest anti-virus programs.
- Regular technical assessment is done to make sure that all the security systems are working seamlessly.
- Damaged/unwanted or duplicate medical records are shredded immediately.
- The premises have maximum security with 24/7 security personnel.
A medical transcription outsourcing provider with long-term experience in the field will make sure that all healthcare data entrusted to them remain private and confidential. Healthcare providers looking to utilize transcription service must take special care to understand the various security and confidentiality practices of their partnering agency.